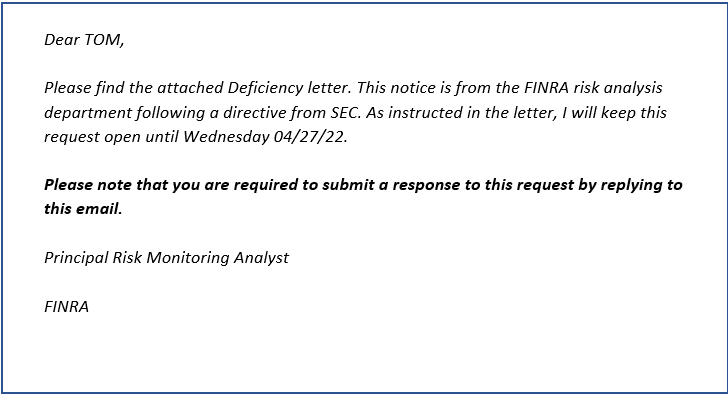
It was brought recently to our attention that many of our investment adviser clients have received a suspicious email similar to the sample below. This email appears to be sent from the email domain: claims-finra.org and includes a subject line such as “Re: FINRA URGENT REQUEST FOR….”
This has been reported to the FINRA IARD system and their instructions are to DELETE THE MESSAGE. FINRA is aware of the email as their voice message reports as of 4/25/2022. You may contact the IARD Help Center if you have any additional follow-up questions (240) 386-4848.
We strongly recommend that you refrain from replying to or clicking upon any links within this phishing email from @claims-finra.org. Additionally, you should notify all employees and personnel that such FINRA imposter emails are circulating and instruct staff not to reply to the email, refrain from clicking upon any links with the email and delete such email.
To the extent any of your staff replied to or clicked upon the phishing email, you should discuss with your information security staff and consultants about whether to implement the following best practices.
- Activate Incident Response Plan.
- Retain Cybersecurity Expert.
- Interview Replier(s)/Clicker(s). You and your cybersecurity expert should ask any and all repliers and clickers what happened, what they saw and if anything strange or out of place occurred after interacting with the phish.
- Obtain Copy of Email. Your cybersecurity expert should obtain the phishing email with full headers showing routing info especially the IP routing address that the phishing message came from (which will be a compromised machine).
- Mine Web for Threat Intelligence. Your cybersecurity expert will take the URLs and attachments to a sandbox and lookup sites. You should not go to the malicious site – do not paste the URL in your browser.
- Search Internal Systems. Your cybersecurity expert will need to check firewall logs to see if there was any traffic leaving your network to suspicious IPs or URLs. Additionally, your cybersecurity expert will need to search DNS logs and DHCP logs. Keep copies of logs.
- Check for Active Sessions. Your cybersecurity expert should check to make sure that the affected users don’t have active sessions. Look for VPNs and Citrix connections and whether they should be active.
- Review Mail Server Logs. Your cybersecurity expert should check to see which users received the message by searching your mail server logs. Search on message ID, source IPs, From, Subject and file attachment name.
- Adjust Email Filters. In order to avoid other users from falling victim to same attack, look for attributes in the email that you can filter for the firm’s email accounts.
- Change Passwords. If your investment adviser firm’s supervised persons or clients clicked the wrong link or provided information in response to a phishing scam, the passwords of the applicable individual(s) should be changed immediately on all of the individual’s accounts. The individual should create unique, non-dictionary, complicated, long (20 characters) passwords.
- Unique Passwords. Require use of unique password- especially do not permit use of same password throughout systems.
- Long Passwords. Require the unique password to be a non-dictionary alpha-numeric password of at least 20 characters/digits long (the longer, the better). A weak password isn’t acceptable even if you utilize two-factor authentication.
- Problematic Password Practices. Avoid using word “password” or derivative such as “passw@rd” in the password. Do not use birthdates, addresses or family member names in passwords. Refrain from using one simple word password like “monkey” or “football” for example. Do not place special characters (e.g., @, #, $) only at beginning or end of password. Password should not include common patterns.
- Password Encryption. Require use of encrypted password manager/database. (Some experts are concerned about encrypted password manager being hacked.)
- Two-Factor Authentication to Access Email from New Device. Turn-on two-factor authentication to access email account from a new device or outside of the network. Certain security experts believe its preferable/safer to receive 2nd factor by special authenticator app (e.g., Google Authenticator, Authy, Microsoft Authenticator) rather than by text due to risk of a mobile phone’s SIM becoming compromised or the text message being intercepted. Check Regularly Accounts.
The above list of actions is by no means an exhaustive one. It is merely a starting point. You should seek advice from a cybersecurity expert on how to respond to becoming a victim of a phishing attack.
Resources
The following resources are best practices that an investment adviser should discuss with its information security staff and consultants.
How to Avoid Phishing Scams Employee Training
Cybersecurity Best Practices Checklist
Cybersecurity – Best Practices for Avoiding and Responding to Phishing Attacks
Cybersecurity – Phishing Email – Letter Notifying Client
Information Security Disclosure
RIA Compliance Consultants, Inc. is not an expert in information security. Our employees are not trained or certified in information security. We do not provide information security risk assessments or audits of information security plans. RIA Compliance Consultants, Inc. offers the above best practices and techniques for the reader to start a discussion with his or her IT & information security staff or consultants.
General Disclosure
The information contained in this blog post is general in nature intended for educational purposes only and is not intended to be a comprehensive analysis of this topic. It is not intended to constitute compliance consulting advice or apply to any particular investment adviser firm’s specific situation. Please consult the applicable securities regulator’s rules and published guidance for more details about the topics referenced above. For more information about the limitations of this blog post and information on our website, please see our Disclosures webpage.
Posted by RCC
Labels: Cybersecurity, FINRA
Tagged: Cybersecurity, FINRA, Phishing